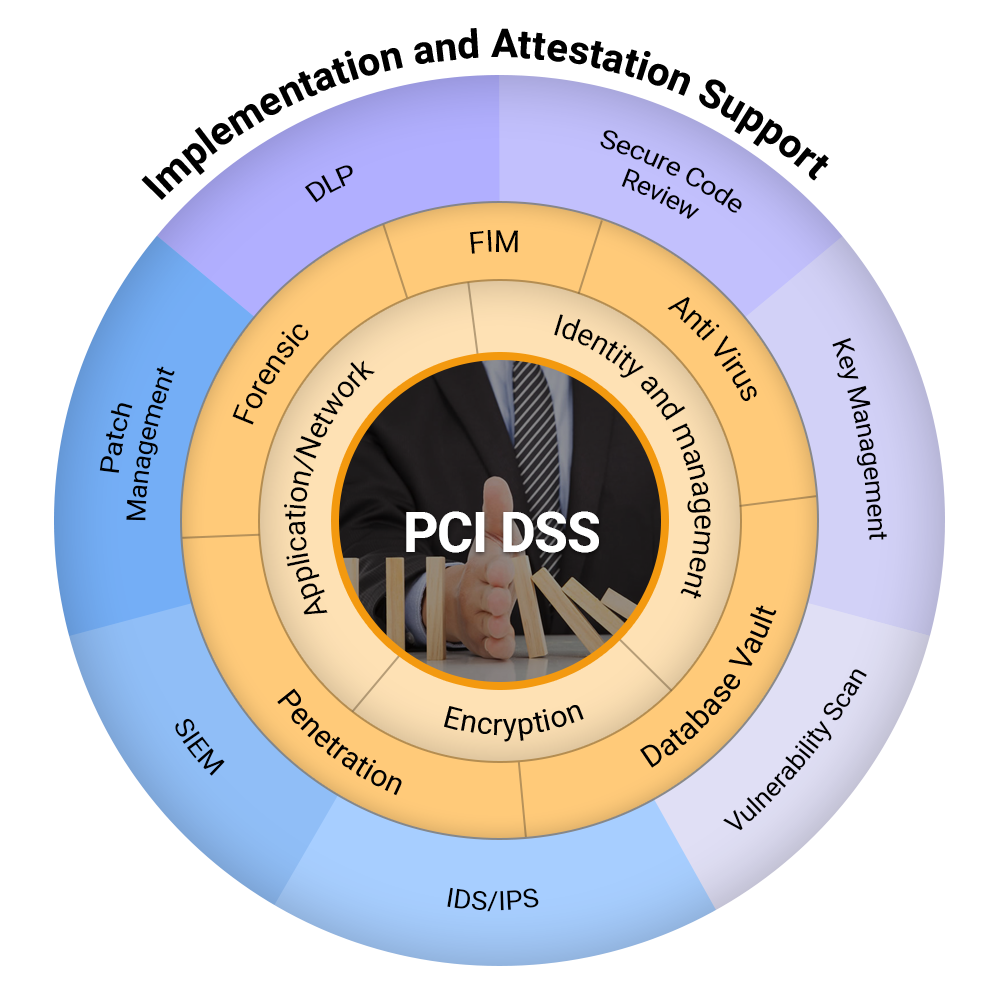
PCI DSS is a globally recognized security standard designed to protect payment card data. It requires businesses that store, process, or transmit cardholder information to implement strong security controls, reduce fraud risk, and safeguard sensitive data across all systems and processes.
Achieving PCI DSS certification significantly reduces the risk of breaches, strengthens customer trust, enhances brand credibility, and supports compliance with industry requirements—helping organizations avoid costly fines, fraud losses, and reputational damage.
Coral has been advising clients since 2010, offering deep expertise, accelerated compliance, and fewer security gaps. Our proven methodologies help organizations avoid costly missteps, strengthen payment data protection, streamline audits, and achieve a smooth, successful certification tailored to their needs.
Questions or clarifications on PCI DSS scope, implementation and attestation? Contact us for a no-obligation conversation.