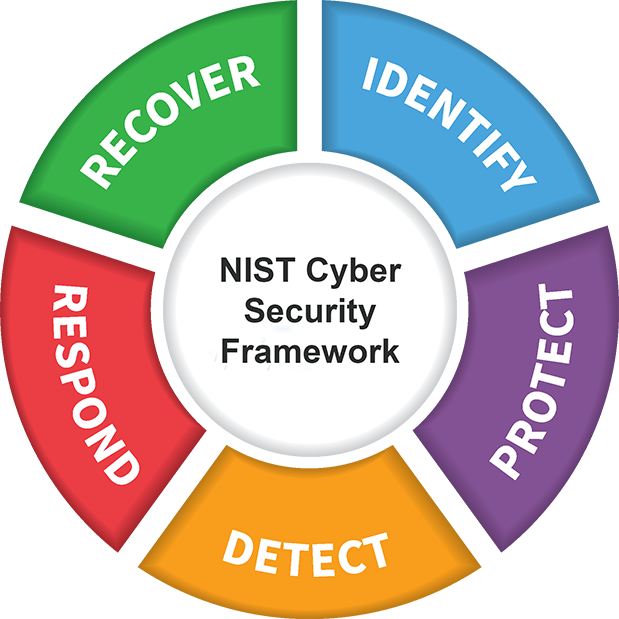
The NIST Cybersecurity Framework (NIST CSF) provides a flexible, risk-based approach to identifying, protecting against, detecting, responding to, and recovering from cybersecurity threats. The latest release—NIST CSF 2.0—expands the framework with a new Govern function and stronger guidance for supply chain and third-party risks.
Implementing NIST CSF strengthens resilience, aligns cybersecurity with business objectives, improves customer trust, and supports compliance with multiple regulatory requirements.
With Coral’s proven NIST expertise, we help organisations accelerate implementation, close security gaps, streamline compliance, and build a mature, resilient cybersecurity program that delivers measurable results. Our methodologies save time, reduce risk, and ensure a smooth, successful adoption of NIST best practices.
Questions or clarifications about NIST CSF implementation or audit? Contact us today for a no-obligation conversation.