SOC 2 and ISO 27001 Integrated Implementation Journey: One Framework, Multiple Outcomes
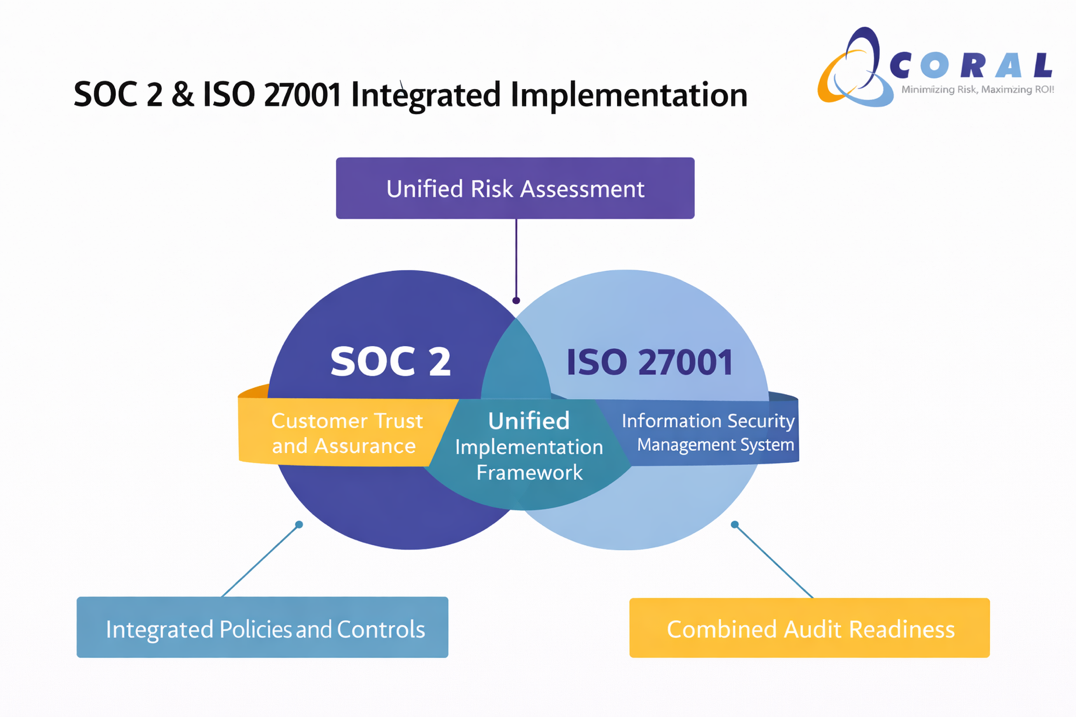
Organizations today are increasingly required to demonstrate strong security and governance across multiple frameworks. While SOC 2 is driven by customer assurance and audit reporting, ISO 27001 focuses on building a comprehensive management system.
Rather than approaching them separately, leading organizations are integrating both into a single, risk-driven governance model—reducing duplication while strengthening overall security.
At Coral eSecure, we guide organizations through a unified journey where SOC 2 and ISO 27001 complement each other.
Step 1: Define Scope and Business Objectives
The journey begins with clearly defining:
- Business services and systems in scope
- Customer expectations (SOC 2)
- Organizational security objectives (ISO 27001)
SOC 2 emphasizes what services are being assured, while ISO 27001 ensures how security is managed across the organization. A combined scoping exercise avoids gaps and overlaps.
Step 2: Unified Gap Assessment and Risk Framework
A consolidated gap assessment is performed across both frameworks.
- ISO 27001 drives a comprehensive risk assessment across all information assets
- SOC 2 aligns these risks to Trust Services Criteria (Security, Availability, etc.)
This creates a single risk register, eliminating the need for parallel efforts and ensuring that controls are both risk-driven and audit-relevant.
Step 3: Control Design and Policy Framework
Instead of building separate controls:
- ISO 27001 provides the management system structure (policies, procedures, governance)
- SOC 2 maps these controls to audit-ready control objectives
Organizations develop:
- Access control, change management, and incident response processes
- Data protection and monitoring mechanisms
- Supplier and third-party controls
This ensures controls are implemented once but satisfy multiple frameworks.
Step 4: Implementation and Operationalization
Controls are embedded across people, processes, and technology.
- ISO 27001 ensures organization-wide adoption and accountability
- SOC 2 requires evidence of control execution over time
This phase focuses on:
- Control ownership across teams
- Training and awareness
- Evidence collection mechanisms
The result is a system that is not just documented, but actively functioning.
Step 5: Monitoring, Internal Audit, and Readiness
Continuous monitoring is critical for both frameworks:
- ISO 27001 requires measurement, internal audits, and management reviews
- SOC 2 requires demonstrable control effectiveness over a period
Internal audits validate both compliance and operational effectiveness, ensuring readiness for certification and attestation.
Step 6: Certification and Attestation
- ISO 27001 certification validates the management system
- SOC 2 report validates the control effectiveness for customers
Together, they provide a powerful combination of governance + assurance.
Beyond Compliance: A Strategic Advantage
Organizations integrating SOC 2 and ISO 27001 achieve:
- Faster implementation with reduced duplication
- Stronger governance and accountability
- Improved customer trust and audit readiness
- A scalable framework for future compliance
At Coral eSecure, we believe integration is not just efficient—it is essential. A unified approach transforms compliance from a checklist exercise into a sustainable, risk-driven governance system aligned with business growth.

